You may use the Resolve-DnsName Microsoft Windows PowerShell cmdlet to perform Domain Name System (DNS) query resolution for the domain name(s) you specify. Below you will find a few examples of this cmdlet.
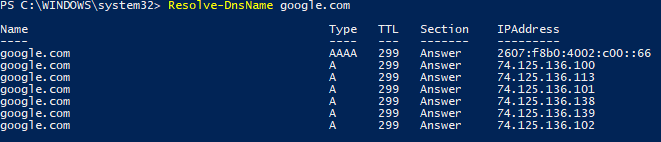
To perform a standard query enter Resolve-DnsName domain.com.
To perform a query without the use of a local hosts file or DNS cache enter Resolve-DnsName domain.com -NoHostsFile.
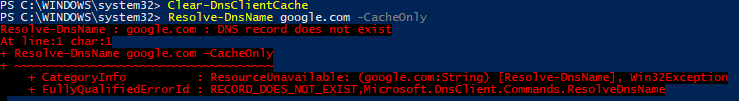
To perform a query only using the DNS client cache enter Resolve-DnsName domain.com -CacheOnly. NOTE: In this example, the DNS client cache is cleared, first. Therefore, the error is expected.
To perform a query while specifying a particular DNS server enter Resolve-DnsName domain.com -Server X.X.X.X.
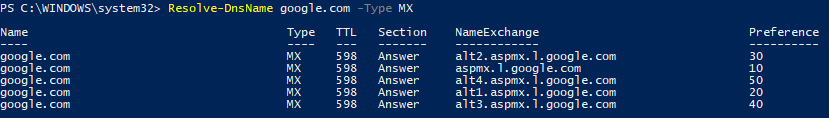
To perform a query for a specific DNS record enter Resolve-DnsName domain.com -Type XX.
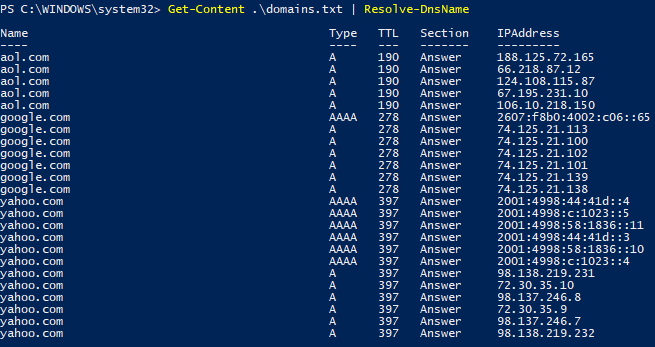
To perform a query of multiple domains enter “domain.com“,”domain.com“,”domain.com” | Resolve-DnsName. 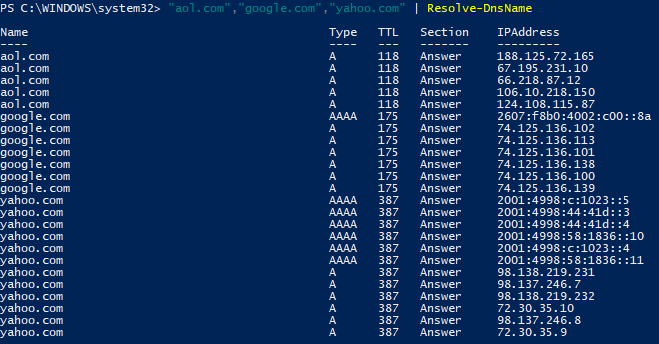
To perform a query of domain names using a file enter Get-Content file | Resolve-DnsName. NOTE: I do not recommend placing the file in the C:\Windows\System32 directory. However, I used that directory in this example for simplicity.